Proactive IT ServicesThat Exceed Expectations
Streamline your business with Online Computers. Our expert IT and marketing services optimize your technology and drive digital growth. We’ve helped hundreds of businesses nationwide manage their tech and thrive online.


About Us
Reliable IT Service Provider with aDevoted Service Touch
Continents
Technology Specialists
Servers Maintained
IT Solutions
Tailored,Reliable & Efficient
Managed IT services
Boost productivity with monthly bundles of customized IT services and support.
IT Support
Minimize downtime and maximize productivity with fast, responsive, and affordable tech support.
IT Consulting
Increase ROI and optimize operations with strategic guidance and end-to-end IT project management.
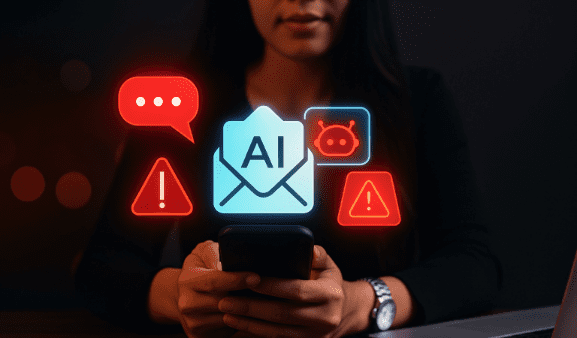
Cybersecurity
Safeguard against threats and secure your data with modern protection tools and 24/7 monitoring.
Cloud Services
Enhance agility, data security, and cost efficiency with powerful cloud-based apps and platforms.
HIPAA Compliance
Ensure compliance with risk assessments, incident management, and other essential services.
Your Trusted Partner
Why ChooseUs?
Profitable Investments
We make sure your tech investments yield quantifiable outcomes for sustained growth. With our proactive IT solutions, cloud services, data security, and desktop management, you can maximize return on investment.
Client Focus
Our team of 50+ technology experts guarantees seamless operations with zero downtime. With our support, you can concentrate on growing your company while we effectively manage your IT requirements.
Successful Partnerships
We manage IT for over 10,000 end users who trust us with their technology needs. Our team provides real-time support and builds long-lasting partnerships with businesses, schools, and nonprofits.
Technology Utilizations
We focus on innovation to drive your success as we grow together. We implement new technology to enhance your business processes, tailoring our solutions to align with your goals.
Dedicated Support
When technology issues arise, we provide timely solutions to minimize disruptions. As your trusted IT partner, we educate, collaborate, and resolve problems to keep your business thriving.
Designed to Modernize Business Processes
01
Software & Data Optimization
02
03
04
Marketing Services
For Strategic MarketingExcellence
Blog
Insights andResources
Subscribe to Our Newsletter
Testimonials